
Managing Director, Netrika Consulting India Pvt Ltd, ASIS APAC Board Member
CFE, CII, FCIISCM, CATS, CCPS, CFAP

Managing Director, Netrika Consulting India Pvt Ltd, ASIS APAC Board Member
CFE, CII, FCIISCM, CATS, CCPS, CFAP

Director – Forensic Investigation
CII
Digital forensics is a branch of forensic science that focuses on identifying, acquiring, processing, analysing, and reporting data stored electronically. Electronic evidence plays a key role in most criminal activities, and digital forensics is essential for supporting law enforcement investigations.
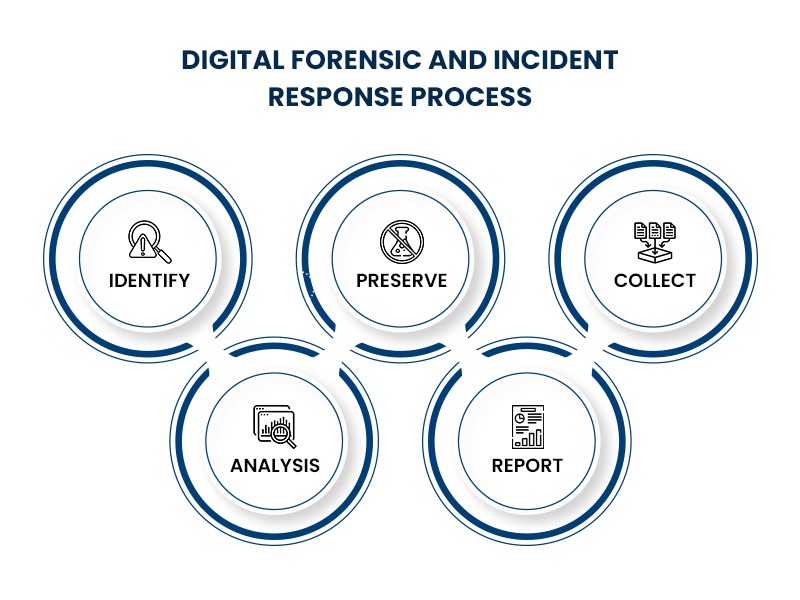
Digital forensics and incident response (DFIR) is a specialized field that focuses on identifying, addressing, and investigating cybersecurity incidents. As the name suggests, DFIR has two related components: Digital forensics involves collecting, preserving, and analyzing forensic evidence and Incident Response is a systematic process designed to address and resolve cybersecurity threats or data breaches.
Digital forensics and incident response (DFIR) is a rapidly growing field that demands dynamic thinking and a novel approach. Combining digital investigation services with incident response expertise is critical for managing the increasing complexity of modern cybersecurity incidents.
DFIR provides a deep understanding of cybersecurity incidents through a comprehensive forensic process. DFIR experts gather and investigate vast amounts of data to fill in gaps of information about cyberattacks, such as who the attackers were, how they broke in, and the exact steps they took to put the systems at risk.
Today's evolving business landscape is characterised by increasing digitisation, a shift to cloud computing and relentless cyber threats penetrating even the most cutting-edge systems. Given the volatility of the market, environmental issues, human error, and the massive volume of information, businesses cannot escape the risks waiting to attack and exploit their vulnerabilities.
Digital Forensics and Incident Response (DFIR) is a field within cybersecurity that focuses on the identification, investigation, and remediation of cyberattacks. This persistent issue has raised the demand for robust digital forensics and incident response strategies for organisations, regardless of their size and capacity.
Digital Forensics and Incident Response (DFIR) is a multidisciplinary approach that combines the dynamics of uncovering the truth behind a cyberattack and responding to it in an efficient and swift manner. DFIR is a specialised field focused on identifying, remediating, and investigating cybersecurity incidents. As the name suggests, DFIR consists of two components: Digital forensics involves collecting, preserving, and analyzing forensic evidence. More broadly DFIR covers:
Digital forensics and incident response work together to help businesses stay informed and prevent issues like cyber threats, data breaches, reputational harm, disruptions to business operations, and legal compliance challenges.
As remote and hybrid work culture grows, a strong DFIR strategy is crucial for organisations to maintain security, investigate, incidents effectively, identify vulnerabilities, minimize operational disruptions, recover quickly from cyber threats, and limit the impacts of attacks to a small area.
Organisations that depend on digital systems for data creation and processing are facing an increasing number of sophisticated threats, such as advanced persistent threats (APT), ransomware attacks, and online identity risks.
Today, businesses must equip themselves with advanced digital forensics and incident response capabilities for both on-premise and cloud environments. These capabilities allow for quick detection, thorough analysis, and fast reponses to incidents, ensuring strong protection is in place.
Netrika’s Digital Forensics and Incident Response Services (DFIR) offer a complete set of capabilities that identify gaps in existing security and help businesses predict, detect, and mitigate security incidents.
DFIR is a digital emergency response field focused on identifying, investigating, and addressing cyberattacks and cybercrimes. It examines system data, user activity, and other digital traces to gather evidence and understand the sequence of events in any negative incident (such as an attack, breach, fraud, or crime.)
Digital Forensics: As a subset of forensic investigation, it examines system data, user actions, and digital evidence to identify ongoing attacks and determine the identities behind them.
Incident Response: This approach outlines an organisation's strategy for preparing in advance, quickly detecting, efficiently containing and systematically recovering from potential data breaches.
Using advanced tools, our DF experts help businesses respond to digital fraud, malware infections, hacker attacks, data theft, and other unwanted digital activities. Our professionals examine data on digital assets across computers, mobile phones, enterprise networks, cloud environments, and the surface, dark, and deep web. They can thoroughly investigate the root cause of any incident.
Recover critical digital evidence to support your investigation with our industry-leading forensics team.
● Extraction & Analysis of Data
Detailed data extraction and analysis reveal important insights from complex digital environments, helping investigators uncover hidden facts and build accurate investigative narratives.
● Disk Imaging & Investigation
A disk image is a complete copy of a storage device, including visible data, hidden directories, boot records, partition tables, deleted files, and unallocated sectors. Netrika uses advanced tools to create accurate hard disk copies, which can be analysed with specialised forensic tools to extract evidence.
● Mobile Forensics (Android/Apple)
Mobile phone forensics is a systematic digital investigation method used to thoroughly examine mobile phones (Android/iphones), tablets, and satellite navigation devices, along with their associated media, such as SIM cards and memory storage cards.
● Cloud-based analysis
Our cloud-based analysis uses advanced technology to examine digital data stored in cloud environments. This efficient approach helps organisations make informed decisions and optimise strategies based on real-time information, driving agility and innovation in today's dynamic business landscape.
● E-mail Investigation
Email forensics helps examine email sources and content for evidence, using various methods to investigate email related offenses. Our experts analyse header data from relevant messages, carefully decode important details after tracking suspects, and complete the email forensic investigation to strengthen your case.
● Social Media Discovery
Social media evidence is a new and rapidly emerging area in digital forensics. If properly explored, the data trail on social media can provide valuable support in cases. By following the correct legal and scientific procedures, Netrika analyses social media to examine and present data as evidence in court.
Netrika delves into social media to examine and present data for evidentiary purposes in court.
● Network Forensics & Analysis
Network forensics involves examining network traffic to investigate potential malicious activities. With network forensics, all data can be retrieved, including messages, file transfers, emails, and web browsing history, and reconstructed to reveal the original transaction.
● Video/Image Forensics
Through our Audio and Video Forensic services, we enhance the value and effectiveness of visual evidence. Our advanced forensic facilities enable secure media extraction from devices, including CCTV enhancement and audio analysis. These processes provide strong evidence that supports criminal or civil cases.
● Forensics and Investigation Training
The growing impact of fraud and corruption, along with the methods used, requires a strong response through careful, fact based investigations. Gain a practical, in-depth understanding of investigative procedures through our comprehensive training program. Designed not only for internal investigators and loss prevention teams, it is also valuable for those involved in forensic assessments within internal audit, risk, or compliance roles.
Digital Forensic and Incident Response (DFIR) aids incident response through:
● Speed and Efficacy
● Efficient & Tailored Approach
● Commercial & OSINT Tools/Technology
● Standards-based Methodology/Approach
● Post Breach Monitoring with Alerts/Notifications
Our Products/ Tools
Digital devices are everywhere and play a key role in chain-of-evidence investigations. Today, the crucial evidence is more likely to be found on a laptop or phone than on a physical weapon. Whether linked to a suspect or a victim, these devices store vast amounts of data that can help investigators build a strong case.
Retrieving data securely, efficiently, and lawfully can be complex. For this reason, our investigators rely on the latest digital forensics tools to assist them.
- Advance Mobile Forensic
Teel Technologies JTAG, ISP and Chip-Off
JTAG forensics involves connecting the Test Access Ports (TAPs) on a PCB using solder, Molex, or a jig. It uses supported JTAG boxes (such as Riff, Z3X, ATF, etc.) to control the processor and retrieve raw data stored on the connected memory chip, creating a complete physical image of the device. This process is non-destructive to the phone.
Complete JTAG kits, which include JTAG boxes, jigs, and accessories like GPG, RIFF, ORT, Octoplus, and ATF, along with over 50 jigs, JTAG finders, and other tools.
- Advance Level Hard Disk Forensic
ACE Lab
ACE is a trendsetter in developing professional tools for HDD repair and data recovery. Through its PC-3000 product line, ACE creates advanced data recovery technologies and provides customers with the most reliable professional tools. By continuously improving its tools, ACE has set the standard for data recovery and remains the proven leader in the field.
- DVR Examination Tool
DVR Examiner
DVR Examiner lets you connect directly to a DVR hard drive or forensic image, bypassing passwords and complex menus. It also helps recover data from damaged, burnt, or broken DVRs.
- Hard Disk Analysis Tools
Belkasoft Evidence Centre
Belkasoft X allows data acquisition from computers, laptops, and mobile devices. It can acquire data from hard and removable drives in DD and E01 formats, with optional hash calculation and verification. For iOS devices, it can acquire iTunes backups and complete file system copies using agent-based or checkm8 methods, or when the device is jailbroken. Android devices support multiple formats: standard ADB or agent-based backups, EDL, and physical backups for rooted devices.
Belkasoft X performs the acquisition, examination, analysis, and presentation of digital evidence from key sources such as computers, mobile devices, RAM, and cloud services in a forensically sound way.
FTK (Forensic Tool Kit)
With the growth of big data from various devices and systems, finding and collecting relevant evidence quickly and efficiently can be challenging. Whether you're law enforcement facing a growing backlog of devices or a company searching through vast amounts of data from multiple sources, FTK helps reduce investigation time and resources by offering an integrated forensics solution trusted by expert digital investigators.
OpenText Encase
OpenText EnCase Forensic is a powerful, court-tested, market-leading solution designed for digital forensic investigations. It allows examiners to triage, collect, and decrypt evidence from various devices in a forensically sound manner. The built-in, enhanced indexing engine offers fast processing, advanced index searching, and optimized performance. The process is quick, efficient, repeatable, and defensible, with the ability to generate intuitive reports.
Magnet Axiom
Easily recover deleted data and analyse digital evidence from mobile, computer, cloud, and vehicle sources within a single case file using an artifact-first approach. Discover the full history of a file or artifact to build your case and prove intent. Magnet AXIOM offers the most up-to-date artifact support for the latest devices and sources.
Image Authentication Tool
AMPED Authenticate
Amped Autheticate is a software application for forensic image authentication, tampering detection, and camera ballistics on digital images. It is the only image authentication software on the market that offers a comprehensive suite of powerful tools. It allows users to analyse the data behind digital images, including image integrity, authenticity, metadata, source history, and tampering detection, before the images are used as intelligence or evidence.
- Image Enhancement Forensic Tool
AMPED FIVE
Amped FIVE is a comprehensive image processing software designed for forensic lab experts to manage the entire image and video analysis workflow. It offers advanced, customisable tools for conversion, restoration, enhancement, measurement, presentation, and reporting, all in one application.
- Password Forensic Tools
Passware Kit Forensics
Passware forensic products are trusted by top law enforcement agencies worldwide to solve cases that require decryption, with a 70-percent success rate. Passware has helped prevent nuclear terrorism, saved hostages held at gunpoint, and is the go-to tool for law enforcement in combating child exploitation.
- Disk Duplicator
OpenText Disk Duplicator TD4
The OpenText Tableau Forensic TD4 Duplicator is a next-generation, budget -friendly, and easy-to-use solution for standalone forensic acquisitions of standard physical media (PCle, USB, SATA, and SAS). The TD4 offers the perfect balance of features and performance for handling smaller-scale triage, acquisition, and media management tasks.
Falcon Neo
The forensic imaging solution delivers imaging speeds exceeding 50GB/min. With the Falcon-NEO, you can simultaneously image from up to 5 source drives to as many as nine destinations, ensuring efficient and secure digital evidence collection. It supports imaging to and from a network repository with two 10GbE ports. The Falcon-NEO is a forward-thinking solution designed to streamline the evidence collection process.
- MAC Forensic Analysis
Cellebrite Digital Collector
The Cellebrite Digital Collector is the only forensic solution on the market today that supports both live and dead box imaging for Windows and Mac. It is a crucial tool in the digital forensic toolkit, offering powerful imaging software for triage, live data acquisition, and targeted data collection on Windows and Mac computers.
The Digital Collector is designed for investigators to perform quick triage and analysis, whether on-scene or in the lab, while maintaining the reliability they trust from Cellebrite.
Cellebrite Inspector
Cellebrite Inspector is used worldwide to analyse computer extractions quickly and thoroughly. It efficiently finds internet history, downloads, recent searches, top sites, locations, media, messages, recycle bins, USB connections, and more. With AI-assisted picture and video categorisation, powerful filtering, and support for the latest systems for full disk encryption, Cellebrite Inspector can display an event's timeline and uncover the real story behind each case.
- E-mail Analysis
Paraben E-mail Examiner
The E3 Forensic Platform seamlessly integrates a wide range of evidence into a single interface for searching, parsing, reviewing, and reporting on digital data from most digital sources. Email processing can be done with local archives using E3: EMX, network archives with E3:NEMX, or both combined.
Intella PRO
Intella PRO is an ideal email investigation and eDiscovery software tool designed for processing, searching, filtering, and producing large volumes of electronically stored information (ESI). It also features a powerful search engine and unique visual presentation for enhanced data analysis.
- Forensic Workstation
The AntfuAnalyzer series is globally recognized for its speed, reliability, and durability, making it the ideal choice for indexing and processing IT forensic cases in the workplace.
All AntAnalyzer products are certified and tested for compatibility with programs from leading software manufacturers, such as Exterro, OpenText, Magnet Forensics, and others.
- Social Media Analysis
X1 Social Discovery
X1 Social Discovery is the only solution that enables automated item-level collection of Twitter, Tumblr, and Youtube data. It allows all collected data to be analysed in a single interface, supporting filtering and instant searchability of content and metadata from social media, websites, and webmail collections.
- Mobile Forensic Tool
Cellebrite UFED
Cellebrite UFED is the industry standard for lawfully accessing mobile data. It helps bypass locks, perform advanced unlocks, and conduct logical /full file system/physical extractions of app data and cloud tokens, among other features. With support for over 32,000 device profiles, it offers the most comprehensive device coverage for leading Android and Apple devices.
MOBILedit Forensic
MOBILedit Forensic Express is an all-in-one solution for phone and cloud extraction, data analysis, and report generation. This powerful 64-bit application uses both physical and logical data acquisition methods. Forensic Express excels with its advanced application analyser, deleted data recovery, support for a wide range of phones (including most feature phones), fine-tuned reports, concurrent phone processing, and an easy-to-use interface. With the password and PIN breaker, users can access locked ADB or iTunes backups using GPU acceleration and multi-threaded operations for maximum speed.
Cellebrite Responder
Cellebrite Responder empowers investigative teams to securely extract data from a wide range of devices, whether at specific locations or on the go. As a key component of Cellebrite's investigation solutions, it enables users to perform selective or full physical data extraction, saving time and enhancing community trust.
MSAB Office
MSAB Office is an all-purpose forensic system from MSAB, offering the XRY product solutions in a comprehensive package. With MSAB Office, you can recover vital data by delving deeper into mobile devices. Featuring tools for Logical, Physical, Cloud, and pinpoint recovery across all supported devices, the Office kit works on your PC to produce secure forensic reports containing data extractions from mobile handsets.
MSAB Field
MSAB Field is designed for mobile units working in demanding conditions. These users need rugged, portable, self-sufficient forensic kits that are flexible, quick to use, and easy to connect to headquarters or remote computers. The Field Version incorporates all these features, combining hardware and software to perform complete and rapid analysis on the majority of mobile devices available today. It meets the strict specifications of MIL-STD-810G and IP65 compliance for durability and reliability.
MSAB pinpoint
XRY Pinpoint extracts and decodes data from non-standard mobile devices, such as low-cost imitation phones from Asia. Since the connector is often the primary forensic challenge, this solution combines powerful software that automatically detects the pin-out configuration with compact hardware, providing an efficient way to handle these devices.
XRY Pinpoint is fully integrated and utilises the familiar, easy-to-use XRY Logical/Physical interface, though it requires a separate license. It is regularly updated to stay current and improve over time. Pinpoint supports devices with MediaTek, Spreadtrum, Coolsand/RDA, and Infineon chipsets.
Cellebrite Inspector
Cellebrite Inspector is used worldwide by examiners for quick and comprehensive analysis of computer extractions. Examiners can efficiently find internet history, downloads, recent searches, top sites, locations, media, messages, recycle bin data, USB connections, and more. With AI-assisted picture and video categorization, powerful filtering, and support for the latest full disk encryption systems, Cellebrite Inspector presents the complete timeline of an event, revealing the real story behind each case.
Oxygen Forensic Detective
Oxygen Forensics specialises in mobile devices, cloud, drones, and IoT data, offering the most advanced digital forensic data extraction and analytical tools for both criminal and corporate investigations.
The source drives are actively air-cooled by the unique Ice Tray cooling fan beneath the Tableau T356789iu forensic bridge. The aluminum cooling fins also support the cooling process, ensuring that the suspect drives are read at maximum speed without reaching damaging temperature levels.
India’s largest provider of Digital Forensic Service
Detect threats across network endpoints and recover vital digital evidence using advanced technology.
As the business landscape continues to evolve and face security challenges, a strong digital forensics and incident response management strategy is essential for companies to fully embrace the benefits of digital transformation. While business risks are inevitable, leveraging digital forensics and incident response management from a trusted provider can serve as a valuable asset.
Netrika Consulting, recognized as one of the top digital forensic investigators and incident response service providers, has a dedicated team of experts ready to deliver the clarity and resolution your business needs in the face of security challenges. Our DFIR services help prepare your business for the unexpected, uncover the truth behind incidents, conduct thorough forensic analysis, and strengthen your security posture by offering recommendations to address potential threats.
We assist businesses in responding to digital fraud, malware infections, hacker attacks, data theft, and other unwanted digital activities using advanced tools and techniques. With decades of expertise in examining data across digital assets, including computers, mobile phones, enterprise networks, cloud deployments, and the surface, dark, and deep web, our DFIR experts conduct in-depth investigations to uncover the root cause of each incident.
Digital forensics and incident response are branches of cybersecurity that involve identifying, investigating, containing, remediating and potentially testifying related to cyberattacks, litigations or other digital investigations.
Digital forensics and incident response (DFIR) is a specialized field focused on identifying, remediating, and investigating cybersecurity incidents. As the name suggests, DFIR consists of two related components: Digital forensics involves collecting, preserving, and analyzing forensic evidence. Incident Response is a systematic process designed to address and resolve cybersecurity threats or data breaches. It focuses on identifying, assessing, containing, and eliminating incidents while ensuring minimal disruption to operations. This approach also safeguards critical evidence for subsequent analysis and supports swift recovery to normalcy.
Computer forensics is a field of technology that uses investigative techniques to identify and store evidence from a computer device. Often, computer forensics is used to uncover evidence that could be used in a court of law.
DF is a standard based methodology that can allow post-breach monitoring with alerts. It also enables swift reaction in the event of an incident, and the forensically preserved data proves crucial to the investigation and reporting phases.
Digital forensic investigators are professionals who specialize in collecting, analyzing, and preserving electronic evidence to be used in legal proceedings. These investigators are trained in techniques to recover data from computers, mobile devices, and other digital storage media.